In operational technology security, the most revealing insights often come not from dashboards or threat reports but from the questions organisations ask about their own environments. Industrial systems are complex, long-lived, and tightly integrated with physical processes, which means weaknesses frequently appear not as obvious vulnerabilities but as gaps in understanding. One visual resource that captures this idea succinctly is the diagram titled “20 Questions for OT/ICS Cybersecurity,” authored by . Rather than presenting a checklist of controls or a maturity model, the diagram is composed entirely of questions, each aimed at a different dimension of industrial cybersecurity—from visibility and architecture to resilience and workforce readiness.
The diagram has circulated widely within the industrial cybersecurity community precisely because of its simplicity. In a single page it summarises the lines of inquiry that experienced practitioners repeatedly return to when evaluating OT environments. Its format deliberately avoids prescriptive answers. Instead, it exposes the areas where organisations often rely on assumptions rather than verified knowledge. By structuring discussion around questions, the diagram encourages security teams, engineers, and executives to examine the operational realities of their systems before deciding how they should be defended.
Although the graphic itself is not tied to a specific standard, many of the issues it highlights reflect the layered architecture typically associated with industrial control systems. Industrial environments are commonly viewed as a series of interconnected levels that begin with sensors and physical processes, extend through programmable controllers and supervisory systems, and eventually connect to enterprise IT networks. Each layer introduces different types of risk and different operational constraints, which means cybersecurity strategies must adapt accordingly. The twenty prompts in Holcomb’s diagram can therefore be understood as a guided tour through the operational and organisational dimensions of securing these environments.
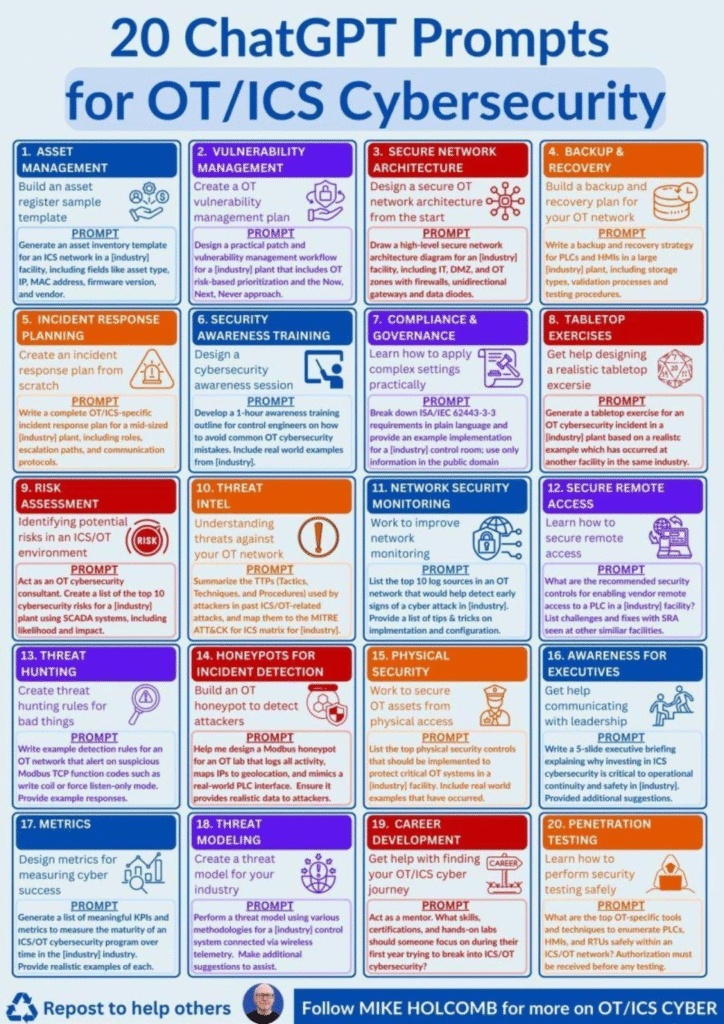
The sections below expand those prompts into analytical questions that CISOs and cybersecurity teams can use when examining their own industrial systems. Each prompt represents a point where misunderstanding or neglect frequently leads to exposure, and each invites deeper investigation into how an organisation’s technology, processes, and people interact.
Prompt 1 — Asset Visibility
Industrial cybersecurity begins with the basic question of whether an organisation truly understands what equipment exists within its operational networks. Unlike enterprise IT systems, industrial assets often remain in service for decades and may have been installed during plant expansions, contractor projects, or emergency repairs that were never fully documented. Controllers, engineering workstations, wireless links, and remote maintenance gateways can therefore exist outside central inventories. Asking how assets are discovered, catalogued, and verified reveals whether security teams are operating with a reliable picture of their environment or relying on outdated documentation that fails to reflect operational reality.
Prompt 2 — Vulnerability Management
In industrial environments vulnerability management cannot be reduced to scanning reports and patch schedules. Controllers and distributed control systems frequently require downtime, vendor approval, or safety validation before updates can be applied. As a result, security teams must evaluate vulnerabilities through the lens of operational impact rather than numerical severity ratings alone. The essential question becomes which vulnerabilities meaningfully threaten production continuity or safety and which can be mitigated through segmentation, monitoring, or compensating controls.
Prompt 3 — Network Architecture
Understanding how industrial networks are actually structured is another critical element of OT security. Architectural diagrams often describe the intended design of a system rather than the connections that exist after years of operational adjustments. Temporary maintenance links, vendor access channels, and monitoring tools can gradually reshape network boundaries. By examining traffic flows and dependencies between systems, organisations can determine whether segmentation strategies remain effective or whether new pathways have introduced unforeseen exposure.
Prompt 4 — Backup and Recovery
Resilience in industrial environments depends on the ability to restore operational control quickly after disruption. Cyber incidents, configuration errors, and equipment failures can all render control systems unavailable, making reliable backups essential. However, the presence of backups alone does not guarantee recoverability. Organisations must determine whether controller configurations, engineering workstation images, and historian data are backed up securely and whether restoration procedures have been tested under conditions that approximate a real incident.
Prompt 5 — Incident Response
Responding to cyber incidents in industrial environments requires coordination between cybersecurity specialists, engineers, and operations personnel. Unlike enterprise networks, where isolating a compromised system is often the first step, abrupt disconnection of industrial systems can create operational instability or safety hazards. Effective incident response planning therefore involves establishing clear communication channels, defining decision authority, and rehearsing scenarios where cybersecurity measures must be balanced against operational continuity.
Prompt 6 — Security Awareness for Engineers
Industrial cybersecurity depends not only on technology but also on the behaviour of the engineers and operators who interact with systems daily. Training programs designed for office workers often fail to resonate with technical staff responsible for industrial processes. Effective awareness initiatives address the specific risks encountered in control environments, such as the security implications of remote vendor access, removable media used for firmware updates, and the handling of engineering laptops connected to control networks.
Prompt 7 — Security Standards in Practice
Standards such as ISA/IEC 62443 provide comprehensive guidance for securing industrial systems, yet translating those frameworks into everyday operational practice can be challenging. Engineers and operators need to understand how requirements for authentication, segmentation, and system hardening affect the equipment they manage. Evaluating how standards are interpreted and implemented in the control environment reveals whether compliance efforts have produced genuine security improvements.
Prompt 8 — Tabletop Exercises
Tabletop exercises allow organisations to explore how they would respond to a cyber incident affecting industrial operations before such an event occurs. By simulating realistic scenarios—such as ransomware targeting supervisory systems or unauthorised commands affecting controllers—teams can test communication pathways, decision-making processes, and coordination between operational and security personnel. These exercises often reveal procedural weaknesses that remain hidden during routine operations.
Prompt 9 — Risk Assessment
Risk assessments in industrial cybersecurity must account for the interaction between digital vulnerabilities and physical processes. A cyber intrusion may manipulate sensor readings, alter control logic, or disrupt communications between systems, producing consequences that extend beyond the digital domain. Effective assessments therefore combine cybersecurity expertise with engineering insight to evaluate how cyber events could affect safety, production, and regulatory compliance.
Prompt 10 — Threat Intelligence
Understanding the evolving tactics used by attackers targeting industrial systems allows organisations to anticipate potential threats rather than reacting after incidents occur. Threat intelligence programs analyse patterns observed in previous attacks, including techniques used to gain access, move laterally across networks, and manipulate control systems. Integrating this intelligence into security strategies helps organisations prioritise monitoring and defensive measures that address realistic adversary behaviour.
Prompt 11 — Network Monitoring
Monitoring industrial networks involves observing specialised communication protocols and device interactions that differ significantly from enterprise traffic. Controllers, sensors, and supervisory systems exchange predictable messages under normal conditions, which means deviations from those patterns can indicate malfunction or malicious activity. Effective monitoring strategies therefore rely on understanding the operational baseline of industrial communications.
Prompt 12 — Remote Access Security
Remote connectivity enables vendors and engineers to maintain complex industrial equipment, but it also introduces pathways that attackers may exploit. Secure remote access solutions must therefore balance operational necessity with strong authentication, session monitoring, and access restrictions. Evaluating how remote access is implemented provides insight into whether external connectivity has become a significant attack surface.
Prompt 13 — Threat Hunting
Threat hunting in industrial environments often focuses on identifying unusual behaviour within network protocols or control commands rather than examining endpoint activity alone. Analysts may search for unexpected configuration changes, unauthorised write commands, or communication between devices that normally operate independently. These investigations can reveal subtle indicators of compromise that automated systems might overlook.
Prompt 14 — Deception and Honeypots
Deception technologies can provide valuable intelligence by presenting attackers with simulated industrial devices or networks designed to attract malicious activity. By analysing how adversaries interact with these environments, organisations can gain insights into reconnaissance techniques and exploitation strategies. Such approaches must be carefully designed to avoid confusion with production systems while still offering credible targets.
Prompt 15 — Physical Security
In industrial environments physical access often translates directly into cyber access. Controllers located on factory floors or remote substations may be reachable by contractors, maintenance staff, or intruders if physical protections are weak. Integrating physical security controls with cybersecurity strategies helps prevent unauthorised access to devices, removable media, and network infrastructure.
Prompt 16 — Executive Awareness
Industrial cybersecurity becomes an executive concern when incidents threaten production, safety, or regulatory standing. Communicating these risks effectively requires translating technical vulnerabilities into operational consequences such as downtime, environmental impact, and supply chain disruption. Clear communication ensures that leadership understands the strategic importance of cybersecurity investments.
Prompt 17 — Metrics and Measurement
Measuring the maturity of an industrial cybersecurity program requires metrics that reflect operational resilience rather than purely technical activity. Useful indicators might include the completeness of asset inventories, the proportion of systems monitored for anomalous behaviour, or the time required to detect and respond to suspicious events. Such metrics provide leadership with a meaningful view of security progress.
Prompt 18 — Threat Modelling
Threat modelling allows organisations to examine how attackers might exploit connections between industrial systems and enterprise networks. By analysing potential attack paths—from remote access points to supervisory systems—security teams can identify architectural weaknesses and implement controls that disrupt those pathways before exploitation occurs.
Prompt 19 — Workforce Development
Industrial cybersecurity requires expertise that spans engineering, networking, and security analysis. Building capable teams therefore involves training professionals who understand both industrial processes and cyber defence techniques. Investing in workforce development ensures that organisations possess the knowledge required to manage complex operational environments.
Prompt 20 — Security Testing
Assessing the security of industrial systems must be done carefully to avoid disrupting sensitive equipment. Intrusive scanning or penetration testing can inadvertently interfere with controllers or communication protocols. Safe testing strategies often involve controlled environments, simulation systems, or carefully scheduled assessments during maintenance windows, allowing organisations to evaluate vulnerabilities without jeopardising production.
Taken together, the twenty questions outlined in Holcomb’s diagram provide a concise but powerful framework for examining the cybersecurity posture of industrial environments. By structuring analysis around disciplined inquiry rather than predefined answers, organisations can identify gaps in visibility, architecture, resilience, and governance that might otherwise remain hidden. For CISOs and security professionals responsible for operational technology, such structured questioning offers a practical way to align cybersecurity strategy with the complex realities of industrial operations.
Follow the SPIN IDG WhatsApp Channel for updates across the Smart Pakistan Insights Network covering all of Pakistan’s technology ecosystem.









